TL;DR
DMARC tells receiving servers what to do when SPF or DKIM fails. The wrong policy can get your emails rejected. Here is the correct DMARC setup for cold email domains.
What Is DMARC?
DMARC (Domain-based Message Authentication, Reporting, and Conformance) is a DNS TXT record that completes your email authentication stack on top of SPF and DKIM. It does three critical things:
- 1Tells receiving servers what to do when SPF or DKIM fails (none, quarantine, or reject)
- 2Requires alignment between the From: domain and the domain authenticated by SPF/DKIM
- 3Provides reporting so you can monitor authentication results across all receiving servers
DMARC builds on SPF and DKIM. Without it, receiving servers make their own unpredictable decisions about failed authentication. In our data across 2,000+ cold email domains, domains without DMARC see 8-12% more emails routed to spam compared to properly configured domains. Google and Yahoo explicitly require DMARC records as of 2024 for bulk senders.
DMARC Policy Levels
Understanding the three DMARC policy levels is critical for cold email. Choose the wrong one and your emails get rejected. Here is the complete comparison:
| Policy | DNS Value | What Happens to Failed Emails | Risk Level | When to Use |
|---|---|---|---|---|
| none | p=none | Delivered normally (monitor only) | High. no protection against spoofing | Starting point. use during warmup and initial setup (first 2 weeks) |
| quarantine | p=quarantine | Sent to spam/junk folder | Medium. failed emails still arrive but in spam | After 2-4 weeks. once SPF and DKIM pass consistently |
| reject | p=reject | Blocked entirely, never delivered | Low. maximum protection but no margin for error | After 30+ days. only when fully confident in authentication setup |
Recommended progression for cold email domains: 1. Day 1: Set p=none. monitor authentication results without risking deliverability 2. Day 14-28: Move to p=quarantine. after verifying SPF and DKIM pass consistently on all mailboxes 3. Day 30+: Optionally move to p=reject. most cold emailers stay at p=quarantine permanently
Most cold emailers should stay at p=quarantine. Moving to p=reject provides marginal security benefit but means a single misconfigured DNS record can cause 100% email loss for that domain.
Setting Up DMARC
Add a TXT record to your domain's DNS:
Host/Name: _dmarc Value: v=DMARC1; p=none; rua=mailto:dmarc@yourdomain.com
After warmup (2-4 weeks): v=DMARC1; p=quarantine; pct=100; rua=mailto:dmarc@yourdomain.com
- v=DMARC1. Version (always DMARC1)
- p=none/quarantine/reject. Policy for failed emails
- pct=100. Percentage of emails to apply policy to
- rua=mailto:. Address for aggregate reports
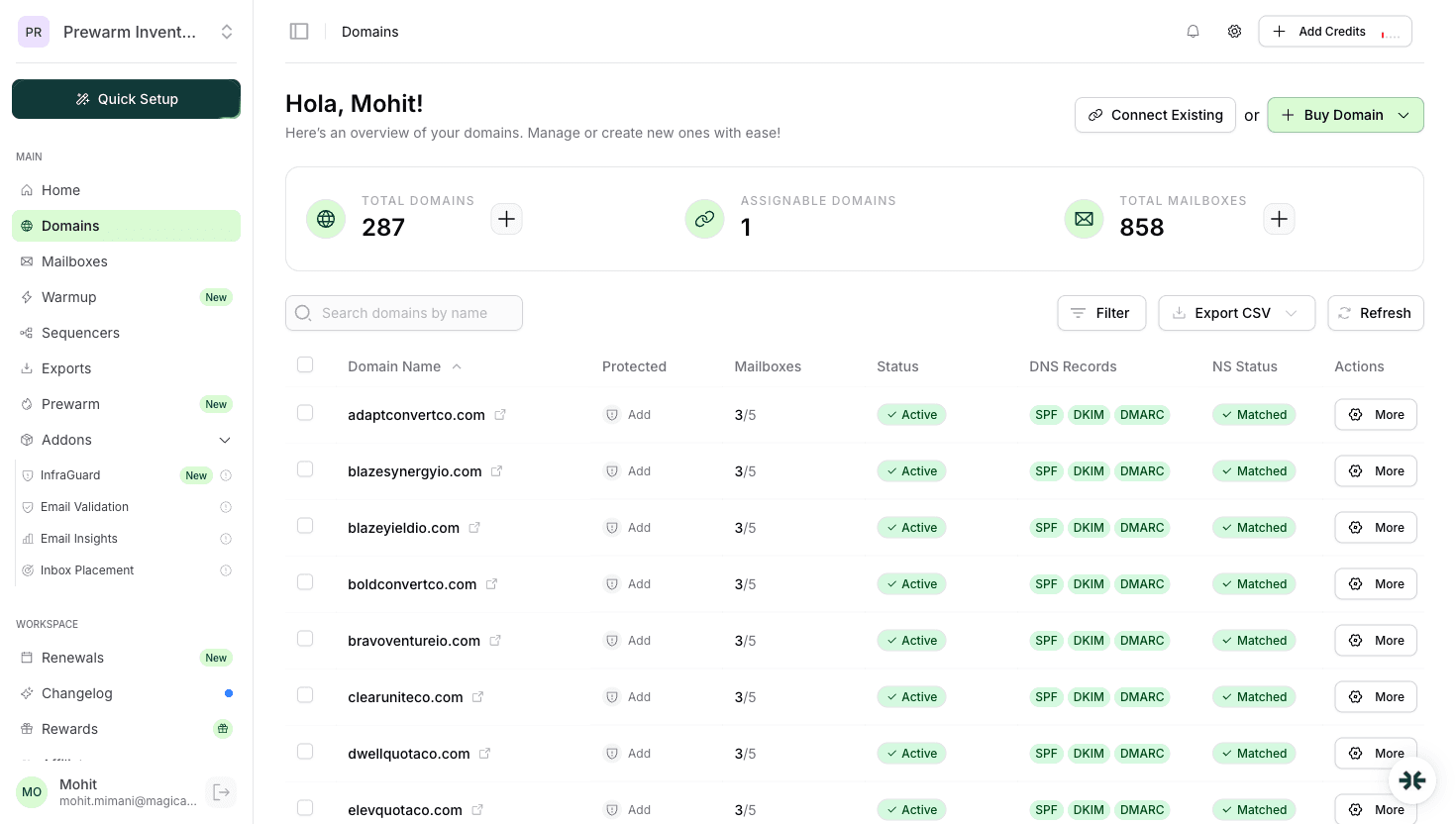
InboxKit sets up DMARC automatically with the correct initial policy.
DMARC for Cold Email Best Practices
- 1Start with p=none during domain warmup period
- 2Move to p=quarantine after verifying SPF and DKIM pass consistently
- 3Do not use p=reject for cold email domains unless you have a specific reason
- 4Set up reporting to monitor authentication results
- 5Use pct=100 to apply the policy to all emails
- 6Monitor alignment. the From domain must match the authenticated domain
DMARC Policy Comparison Table:
| Policy | DNS Value | Action on Failed Emails | Risk Level | Recommended Timeline |
|---|---|---|---|---|
| none | p=none | Monitor only. emails still delivered | High (no protection) | Starting point. first 2 weeks |
| quarantine | p=quarantine | Send to spam/junk folder | Medium | After 2-4 weeks of clean warmup |
| reject | p=reject | Block delivery entirely | Low (maximum protection) | After 30+ days (most cold emailers stay at quarantine) |
InboxKit handles rules 1-4 automatically when you create mailboxes. InfraGuard monitors rule 6 continuously.
Common DMARC Mistakes
1. Starting with p=reject. This rejects any email that fails authentication, including legitimate emails during setup. Start with p=none.
2. No DMARC record at all. Without DMARC, receiving servers make unpredictable decisions about your emails.
3. Forgetting alignment. DMARC requires the From domain to align with SPF and DKIM domains. Misalignment causes failures even when SPF and DKIM individually pass.
4. Not monitoring reports. DMARC reports show authentication failures. Ignoring them means missing configuration issues.
5. Multiple DMARC records. Like SPF, only one DMARC record per domain.
| # | Mistake | Fix |
|---|---|---|
| 1 | p=reject too early | Start p=none, upgrade after 2-4 weeks |
| 2 | No DMARC at all | Add on day 1, even p=none |
| 3 | Alignment mismatch | From: must match auth domain |
| 4 | Ignoring reports | Set rua= and review weekly |
| 5 | Multiple records | One DMARC per domain only |
Automatic DMARC with InboxKit
- Initial setup with p=none for safe warmup
- InfraGuard monitors DMARC alignment continuously
- Alerts if DMARC records are modified or removed
- Guidance on when to upgrade to p=quarantine
No manual DNS editing required.
| Feature | What InboxKit Does | Time Saved |
|---|---|---|
| Initial DMARC | Sets p=none with correct alignment and reporting | 15-30 min/domain |
| SPF/DKIM alignment | Ensures From: domain matches authenticated domain | Eliminates #1 failure cause |
| InfraGuard monitoring | Checks DMARC integrity every few hours | Replaces manual audits |
| Change alerts | Instant notification if records are modified | Catches issues in hours |
For 50 domains, InboxKit saves ~12-15 hours of manual DMARC configuration.
Frequently Asked Questions
Start with p=none during warmup. Move to p=quarantine after 2-4 weeks of clean warmup. Avoid p=reject for cold email domains.
Yes. DMARC is configured automatically with the correct initial policy. InfraGuard monitors it continuously.
Yes. DMARC ties SPF and DKIM together and tells receivers what to do when they fail. Without DMARC, your authentication is incomplete.
Sources & References
Ready to set up your infrastructure?
Plans from $39/mo with 10 mailboxes included. Automated DNS, warmup, and InfraGuard monitoring included.