TL;DR
SPF verifies the sending server, DKIM verifies the message wasn't tampered with, and DMARC tells receivers what to do when checks fail. Here's how they work together with real DNS record examples.
The Three Layers of Email Authentication
Email authentication has three protocols that work together. Each solves a different problem:
| Protocol | What It Verifies | Analogy | DNS Record Type |
|---|---|---|---|
| SPF | Is this server allowed to send for this domain? | Return address on an envelope | TXT at domain root |
| DKIM | Was this message tampered with in transit? | Wax seal on a letter | TXT at selector._domainkey |
| DMARC | What should happen when SPF or DKIM fails? | Instructions to the post office | TXT at _dmarc.domain |
- Without SPF: Receivers can't verify you're authorized to send. Gmail rejects unauthenticated mail since February 2024 (source: blog.google/products/gmail/gmail-security-authentication-spam-protection).
- Without DKIM: Your emails can be modified in transit. Some providers add spam warnings to unsigned messages.
- Without DMARC: You have no control over what happens to spoofed emails using your domain. This damages your domain reputation even if YOU aren't the spammer.
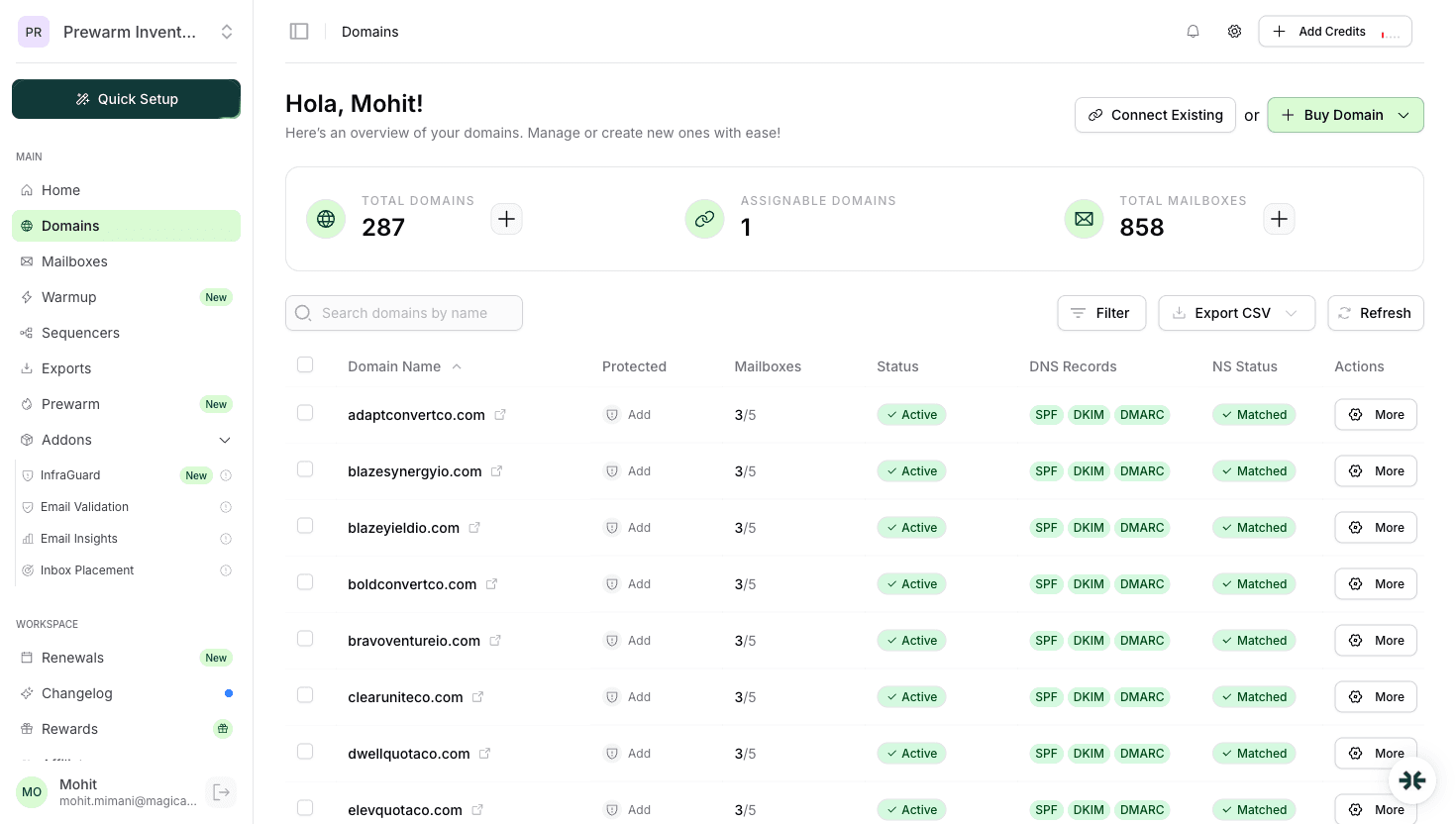
InboxKit configures all three automatically when you add a domain. The screenshot above shows SPF, DKIM, and DMARC green indicators on all active domains.
SPF (Sender Policy Framework)
SPF tells receiving servers which IP addresses and mail servers are authorized to send email on behalf of your domain.
How it works: 1. You publish a TXT record listing authorized senders 2. Receiving server looks up your SPF record 3. Checks if the sending server's IP matches 4. Passes or fails the check
Example SPF records:
| Provider | SPF Record | Source |
|---|---|---|
| Google Workspace | v=spf1 include:_spf.google.com ~all | support.google.com/a/answer/33786 |
| Microsoft 365 | v=spf1 include:spf.protection.outlook.com ~all | learn.microsoft.com/en-us/microsoft-365/security/office-365-security/email-authentication-spf-configure |
| Both (mixed) | v=spf1 include:_spf.google.com include:spf.protection.outlook.com ~all | Combined |
SPF qualifiers explained:
| Qualifier | Meaning | Use Case |
|---|---|---|
+all | Allow everything | Never use. defeats the purpose |
~all | Soft fail (accept but mark) | Recommended during setup |
-all | Hard fail (reject) | Strictest. use after testing |
?all | Neutral | Not recommended |
Common SPF mistake: Having more than 10 DNS lookups. Each include: counts as a lookup. If you exceed 10, SPF fails entirely (source: RFC 7208, Section 4.6.4).
InboxKit's approach: We set the correct SPF record for your mailbox type (Google or Microsoft) automatically. No manual DNS editing required.
DKIM (DomainKeys Identified Mail)
DKIM adds a cryptographic signature to every email you send. The receiving server verifies the signature using your public key published in DNS.
How it works: 1. Your mail server signs each email with a private key 2. The signature is added as a DKIM-Signature header 3. Receiving server retrieves your public key from DNS 4. Verifies the signature matches. proving the email wasn't modified
DKIM key sizes:
| Key Size | Security | Compatibility | Recommendation |
|---|---|---|---|
| 1024-bit | Adequate | Universal | Minimum acceptable |
| 2048-bit | Strong | Most providers | Recommended (Google default) |
| 4096-bit | Very strong | Some DNS limits | Overkill for email |
Source: Google recommends 2048-bit keys (support.google.com/a/answer/174124). Microsoft 365 also uses 2048-bit by default.
What DKIM looks like in DNS:
`
selector._domainkey.yourdomain.com TXT "v=DKIM1; k=rsa; p=MIIBIjAN..."
`
The selector is a label chosen by your email provider. Google uses google as the default selector. Microsoft uses selector1 and selector2.
InboxKit generates and publishes DKIM keys automatically for both Google Workspace and Microsoft 365 accounts during provisioning.
DMARC (Domain-based Message Authentication)
DMARC builds on SPF and DKIM. It tells receiving servers what to do when authentication fails AND sends you reports about who's using your domain to send email.
DMARC policies:
| Policy | Action on Failure | Risk Level | When to Use |
|---|---|---|---|
p=none | Monitor only (deliver anyway) | Reports only | Start here. first 2 weeks |
p=quarantine | Send to spam folder | Medium enforcement | After 2 weeks of clean reports |
p=reject | Block the email entirely | Full enforcement | After 30 days, for maximum protection |
Example DMARC records:
| Stage | Record | What Happens |
|---|---|---|
| Monitoring | v=DMARC1; p=none; rua=mailto:dmarc@yourdomain.com | Collect reports, deliver all mail |
| Gradual | v=DMARC1; p=quarantine; pct=50; rua=mailto:dmarc@yourdomain.com | Quarantine 50% of failing mail |
| Full | v=DMARC1; p=reject; rua=mailto:dmarc@yourdomain.com | Block all failing mail |
Source: Google requires at minimum p=none for bulk senders since February 2024 (support.google.com/a/answer/2466580). The RFC is at tools.ietf.org/html/rfc7489.
DMARC alignment: DMARC checks that the domain in the From header aligns with either SPF or DKIM. There are two modes:
| Mode | SPF Check | DKIM Check | Strictness |
|---|---|---|---|
Relaxed (aspf=r) | Subdomain OK | Subdomain OK | Default, recommended |
Strict (aspf=s) | Exact match only | Exact match only | Can break forwarding |
InboxKit sets p=none by default during domain setup, giving you monitoring without risk. You can upgrade to p=quarantine or p=reject through the dashboard once you've verified no legitimate mail is failing.
How SPF + DKIM + DMARC Work Together
The three protocols create a chain of trust:
| Step | Check | Question Answered | If It Fails |
|---|---|---|---|
| 1 | SPF | Is this server authorized? | DMARC policy applies |
| 2 | DKIM | Was the message modified? | DMARC policy applies |
| 3 | DMARC Alignment | Does the From domain match? | DMARC policy applies |
| 4 | DMARC Policy | What to do with failures? | none/quarantine/reject |
- SPF passes AND aligns with From domain, OR
- DKIM passes AND aligns with From domain
It doesn't need both. just one aligned pass is enough. This is important because email forwarding often breaks SPF but preserves DKIM.
Impact on deliverability (from Validity 2025 Benchmark Report):
| Authentication Level | Average Inbox Placement | Source |
|---|---|---|
| None | 23-45% | Validity 2025 |
| SPF only | 55-70% | Validity 2025 |
| SPF + DKIM | 72-85% | Validity 2025 |
| SPF + DKIM + DMARC (reject) | 85-95% | Validity 2025 / InboxKit data |
The difference between no authentication and full authentication is ~60 percentage points of inbox placement. For cold email, this is the difference between campaigns that work and campaigns that go entirely to spam.
InboxKit automates the entire chain. Every domain gets SPF, DKIM, and DMARC configured in under 10 minutes. The domains dashboard shows real-time status for all three protocols across every domain (see screenshot).
Frequently Asked Questions
Yes. Google requires SPF or DKIM for all senders, and DMARC for bulk senders (5,000+/day). For cold email, you should have all three. InboxKit configures them automatically.
The email can still pass DMARC if the DKIM domain aligns with the From domain. This is common with forwarded emails where SPF breaks but DKIM signature survives.
Typically 15 minutes to 48 hours, depending on TTL settings. InboxKit domains usually propagate within 30 minutes because we use low TTL values during initial setup.
Yes. Use: v=spf1 include:_spf.google.com include:spf.protection.outlook.com ~all. Just make sure total DNS lookups stay under 10 (RFC 7208 limit).
Start with p=none (monitoring). After 2 weeks of clean DMARC reports, move to p=quarantine. After 30 days, move to p=reject for maximum protection. InboxKit starts with p=none by default.
Sources & References
Ready to set up your infrastructure?
Plans from $39/mo with 10 mailboxes included. Automated DNS, warmup, and InfraGuard monitoring included.